Tab Mapper
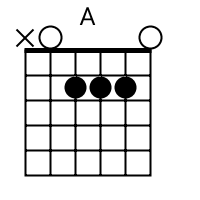
The tab mapper is a handy little tool that will render a guitar tab file with graphic chord diagrams displayed alongside. This comes in handy for people who just don't have every single chord shape memorized. Just plug in the web site address of a valid .tab or .crd file and hit "Go". In general, the tab mapper does a better job with printer friendly URLs. If there is more than one way to play a chord, the tab mapper will choose the most common shape. To see other fingerings, click on the chord diagram and you will be taken to the chord calculator.
Original file located @ https://www.keyanalyzer.com/cyber-security/.
Show me scales that sound good with the chords in this song: A.
- Submit a Guest Post (Write For Us)
- About
- Contact us
Keyanalyzer.com
Menu
- Home
- Crypto
- Proxies
- VPN
- Online Services
- Best Software
- WordPress
- AI Technology
Category: Cyber Security
Is OffGamers Legit? Complete Review and Analysis of the Digital Game Store
jojo Cyber Security, Online Services No Comments
OffGamers is a digital game store that has been operating for over 20 years, but many gamers still question whether it?s legitimate and safe to use. The Singapore-based platform ?
[Continue Reading...]
What Is the Monkey App and Is It Safe to video chat?
jojo Cyber Security No Comments
You have probably heard your teen mention the Monkey app ? or maybe you found it on their phone and started searching for answers. Either way, you are doing the right ?
[Continue Reading...]
Are StockX Shoes Real? The Complete Guide to Authenticity, Verification & Buying Safely
jojo Cyber Security No Comments
You just found a pair of limited-edition Jordans on StockX for a price that seems almost too good to pass up. But before you click ?Buy Now,? one question ?
[Continue Reading...]
Is FitGirl Repacks Safe And Legit? Legal Alternatives
jojo Cyber Security No Comments
You?ve probably heard of FitGirl Repacks. Maybe a friend told you about it. Maybe you stumbled across it while searching for a free game download. And now you?re wondering ?
[Continue Reading...]
Can Ransomware Infect iCloud? Complete Security Guide for Apple Users
jojo Cyber Security, Cloud Storage, Data Security & Privacy No Comments
Ransomware can potentially affect iCloud-stored files if it encrypts files on your Mac or iOS device that automatically sync to iCloud, but Apple?s built-in security features and architectural design ?
[Continue Reading...]
Is Cloud Storage Safe From Ransomware? A Complete Protection Guide
jojo Cyber Security, Cloud Storage, Data Security & Privacy No Comments
Cloud storage can be vulnerable to ransomware attacks, but proper security measures significantly reduce risks and protect your data from encryption threats. Ransomware is malicious software that encrypts your files ?
[Continue Reading...]
How to Enable Windows 11 Ransomware Protection: Complete Guide to Controlled Folder Access and Security Features
jojo Cyber Security, Data Security & Privacy No Comments
Windows 11 includes built-in ransomware protection through Windows Security that blocks unauthorized applications from modifying your important files. This native protection system uses Controlled Folder Access (CFA) to monitor and ?
[Continue Reading...]
What is a Temporary Email Address? Is It Safe for Verification?
jojo Data Security & Privacy, Cyber Security No Comments
You?re signing up for a website and it asks for your email. You don?t really trust the site. Maybe it looks sketchy or you just don?t want spam filling ?
[Continue Reading...]
Does TikTok Detect VPN Usage? Everything You Need to Know
jojo Tiktok, Cyber Security, Data Security & Privacy, VPN No Comments
TikTok blocks users in certain countries and regions. Maybe you?re traveling overseas and can?t watch your favorite videos. Or perhaps TikTok is banned where you live. You might think ?
[Continue Reading...]
Best Practices for Vulnerability Scanning: A Complete Guide to Network Security Assessment in 2025
jojo Network Security, Cyber Security, Data Security & Privacy No Comments
Vulnerability scanning is a way to find security problems in networks, systems, and applications using automated tools and manual checks. Companies today face more cyber threats, making vulnerability scanning ?
[Continue Reading...]
- Previous
Search
Recent Posts
- How to Use Ahrefs for Free: 11 Free SEO Tools
- 8 Best Rank Tracker Tools: Free & Paid Options Tested and Compared
- 12 Best Free RAM Cleaners For Windows 10/11
- 8 Best Free Registry Cleaners Tools to Clean Junk and Registry on Windows PC
- 11 Best Keyword Clustering Tools: Free & Paid Options Tested and Compared
- 11 Best Keyword Generator (Free Keyword Research Tools)
- 12 Top Plumbing Management Software Solutions for 2026
- ServiceTitan Pricing Explained: How Much Does ServiceTitan Cost for Your Business?
- 12 Best Construction Project Management Software For Your Businesses
- The 10 Best Payroll Software for Small Business in 2026
- 17 Best Free Typing Programs to Help You Type Like an Expert
- 10 Best Free & AI Floor Plan Software for Interior Designers (2026)
- 10+ Best Kitchen Design Software For Kitchen Planning Design Using AI
- 20 Best Management Software for Small Business
- Trello vs Jira: Which Project Management Tool Is Right for You in 2026?
- 6 Best Software to Record Mouse and Keyboard Actions and Automate Repetitive Tasks
- 5 Best Free Keylogger Software for Windows 10/11
- The Ultimate Guide to Sending Large Files Online: Top 20 Services for Easy File Sharing
- 6 Best Apps to Track Phone Without Them Knowing
Categories
- AI technology
- AI Tools
- Android Apps
- Best Software
- Bitcoin
- Cloud Storage
- Companies
- Computer Security
- Converter
- Crypto
- Cyber Security
- Data Security & Privacy
- Error
- iPhone
- JavaScript
- Leadership
- Movies
- Network Security
- Online Services
- Proxies
- Python
- Risk Management
- ROMs & Emulators
- SaaS
- SEO Tools
- SMS Services
- Social Media Marketing
- Software
- Technology
- Tiktok
- Unblocked Games
- VPN
- Web Development
- Windows
- WordPress
Ads
Keyanalyzer.com Copyright © 2026.
About - Contact us - Privacy Policy
©2026 JGuitar.com