Tab Mapper
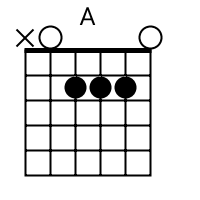
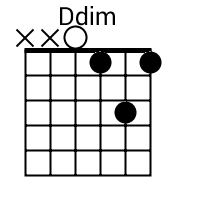
The tab mapper is a handy little tool that will render a guitar tab file with graphic chord diagrams displayed alongside. This comes in handy for people who just don't have every single chord shape memorized. Just plug in the web site address of a valid .tab or .crd file and hit "Go". In general, the tab mapper does a better job with printer friendly URLs. If there is more than one way to play a chord, the tab mapper will choose the most common shape. To see other fingerings, click on the chord diagram and you will be taken to the chord calculator.
Original file located @ https://www.keyanalyzer.com/.
Show me scales that sound good with the chords in this song: A, Do.
- Submit a Guest Post (Write For Us)
- About
- Contact us
Keyanalyzer.com
Menu
- Home
- Crypto
- Proxies
- VPN
- Online Services
- Best Software
- WordPress
- AI Technology
Best Practices for Vulnerability Scanning: A Simple, Real-World Guide to Finding Security Gaps Before Attackers Do
jojo Network Security, Cyber Security, Data Security & Privacy No Comments
If you want vulnerability scanning to work, do not treat it like a button you click once a month. It works when you know what you own, scan the right ?
[Continue Reading...]
Jira vs Hive: Which Project Management Tool is Right for Your Team?
jojo Best Software, Software No Comments
When you need to choose between Jira and Hive for your project management needs, you?re looking at two powerful tools that help teams stay organized and productive. Both platforms ?
[Continue Reading...]
Agile Mobile Development: What It Is, How It Works, and Why Your Team Needs It
jojo Android Apps, SaaS No Comments
Agile mobile development is a way of building mobile apps in short, focused work cycles ? typically 1 to 2 weeks ? where your team delivers working features, collects ?
[Continue Reading...]
How Are Apps Made? The Complete Step-by-Step Process Behind Every App on Your Phone
jojo Android Apps No Comments
You use apps every single day. You wake up to an alarm app. You check a weather app. You scroll through a social media app. You order lunch from ?
[Continue Reading...]
What Is a Cloud Security Scanner for AWS, Azure, and Google Cloud?
jojo Data Security & Privacy, Cloud Storage, Cyber Security No Comments
If you work in the cloud, you need fast answers. You need to know what is exposed, what is weak, and what needs a fix first. That is where ?
[Continue Reading...]
What Is pCloud Crypto? A Real-World Look at Encrypted Cloud Storage
jojo Cloud Storage, Data Security & Privacy No Comments
pCloud Crypto is an optional security layer built on top of pCloud?s cloud storage platform. It gives you a dedicated encrypted folder inside your pCloud account where files are ?
[Continue Reading...]
Is Temu Legit or a Scam? The Complete Truth You Need to Know
jojo Cyber Security, Online Services No Comments
You?ve probably seen the ads everywhere. Temu promises rock-bottom prices on everything from clothing to electronics. But when a deal looks too good to be true, your guard goes ?
[Continue Reading...]
8 Best Cheap Shared Hosting Providers for WordPress In 2026
jojo WordPress No Comments
Cheap shared hosting is essential for anyone who wants to launch a website without exceeding their budget. You get reliable web hosting where your site shares server resources like ?
[Continue Reading...]
15 Free Movie Apps for Android: Your Complete Guide to Legal Streaming in 2026
jojo Online Services, Movies No Comments
Are you tired of paying for expensive streaming subscriptions every month? We understand how frustrating it can be when you just want to watch a good movie without breaking ?
[Continue Reading...]
How to Use Ahrefs for Free: 11 Free SEO Tools
jojo SEO Tools No Comments
Ahrefs can be used for free through 11 free SEO tools ? including Ahrefs Webmaster Tools, Free Keyword Generator, Free Backlink Checker, Free SERP Checker, and AI Visibility Checker ? ?
[Continue Reading...]
- Previous
Search
Recent Posts
- Best Practices for Vulnerability Scanning: A Simple, Real-World Guide to Finding Security Gaps Before Attackers Do
- Jira vs Hive: Which Project Management Tool is Right for Your Team?
- Agile Mobile Development: What It Is, How It Works, and Why Your Team Needs It
- How Are Apps Made? The Complete Step-by-Step Process Behind Every App on Your Phone
- What Is a Cloud Security Scanner for AWS, Azure, and Google Cloud?
- What Is pCloud Crypto? A Real-World Look at Encrypted Cloud Storage
- Is Temu Legit or a Scam? The Complete Truth You Need to Know
- 8 Best Cheap Shared Hosting Providers for WordPress In 2026
- 15 Free Movie Apps for Android: Your Complete Guide to Legal Streaming in 2026
- How to Use Ahrefs for Free: 11 Free SEO Tools
- 8 Best Rank Tracker Tools: Free & Paid Options Tested and Compared
- 12 Best Free RAM Cleaners For Windows 10/11
- 8 Best Free Registry Cleaners Tools to Clean Junk and Registry on Windows PC
- 11 Best Keyword Clustering Tools: Free & Paid Options Tested and Compared
- 11 Best Keyword Generator (Free Keyword Research Tools)
- 12 Top Plumbing Management Software Solutions for 2026
- ServiceTitan Pricing Explained: How Much Does ServiceTitan Cost for Your Business?
- 12 Best Construction Project Management Software For Your Businesses
- The 10 Best Payroll Software for Small Business in 2026
Categories
- AI technology
- AI Tools
- Android Apps
- Best Software
- Bitcoin
- Cloud Storage
- Companies
- Computer Security
- Converter
- Crypto
- Cyber Security
- Data Security & Privacy
- Error
- iPhone
- JavaScript
- Leadership
- Movies
- Network Security
- Online Services
- Proxies
- Python
- Risk Management
- ROMs & Emulators
- SaaS
- SEO Tools
- SMS Services
- Social Media Marketing
- Software
- Technology
- Tiktok
- Unblocked Games
- VPN
- Web Development
- Windows
- WordPress
Ads
Keyanalyzer.com Copyright © 2026.
About - Contact us - Privacy Policy
©2026 JGuitar.com